With the advent of technologies and the demand of modern workplaces, real-time communication is increasing extensively. VoIP is one such solution that fulfills the communication requirement. A VoIP Solution is convenient, flexible, cost-effective, and reliable. However, with the endless benefits of VoIP, significant security risks also take birth. To combat all these security issues of VoIP Solutions, the role of SBC comes to play. A Session Border Controller Solution SBC works on the session level of each VoIP packet and signal while safeguarding communication flows. It ensures greater control and security over the media streams.
This article walks you through the concept of VoIP security, it’s working, the pitfalls of VoIP solutions, and how the SBC solution resolves it to transform the consumer experience.
What Is VoIP?
Voice Over Internet Protocol (VoIP) works on the flow of voice and data over an internet connection. A VoIP Solution is also known as (IP) internet telephony or cloud-based telephony. It allows users to place voice calls from any device, including laptops, desktops, smartphones, VoIP phones, WebRTC-enabled browsers, etc. Most businesses are switching to VoIP Solutions due to their cost-effectiveness and advanced features like call waiting, call routing, auto-attend, and more. However, since VoIP is exposed to the internet, it faces many security threats.
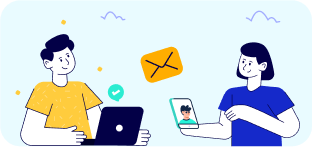
Why Does VoIP Security Matter?
As per a survey by JP Morgan, the top concern of 94% of the business leaders is malware, payment fraud, data breach, and similar infrastructure-related security concerns. If we list out major VoIP issues, call interception, caller ID spoofing, and DoS attacks would top the list.
Another report by IBM also highlights the gravity of this security threat. IBM’s report in 2019 suggests that the cost of security breaches continues to rise yearly. In the United States alone, the cost of the security breach is $8.1 million, which is enormous and requires stringent remedies.
 How Does VoIP System Work?
How Does VoIP System Work?
It is evident, thus far, that VoIP Solution has certain security shortcomings that the Session Border Controller (SBC) takes care of.
Let us dive in deep to understand how does VoIP system work and where SBC enters the game.
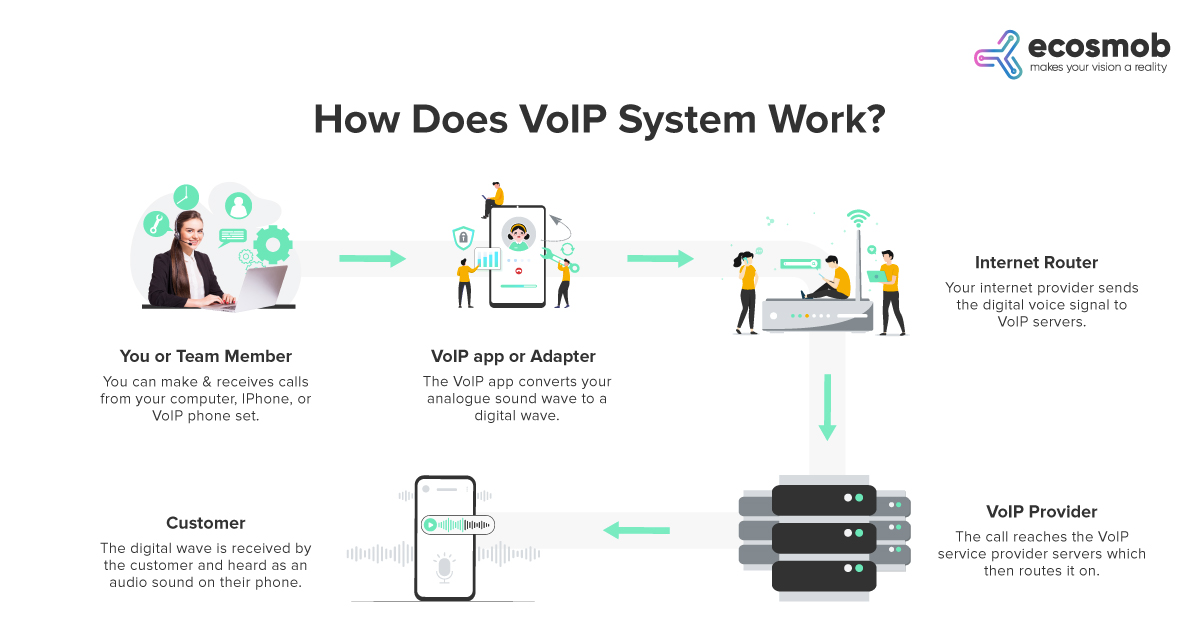 A typical system may have IP phones and standard PSTN phones connected through a server to the internal LAN that connects to the internet. However, VoIP uses SIP and H.323 signaling protocols to set up, manage and terminate calls. The Media Gateway Control Protocol handles the interface between PSTN and VoIP gateways. H.323 includes a set of sub-protocols; for instance –
A typical system may have IP phones and standard PSTN phones connected through a server to the internal LAN that connects to the internet. However, VoIP uses SIP and H.323 signaling protocols to set up, manage and terminate calls. The Media Gateway Control Protocol handles the interface between PSTN and VoIP gateways. H.323 includes a set of sub-protocols; for instance –
- H.225 for call control
- H.235 for security framework and call setup
- H.245 for specifying media paths
- H.450 for supplementary services
Due to multiple sets of protocols, there exist complexity and security loopholes in VoIP Solutions.
So, Can VoIP Be Hacked? The answer is YES!
What Are The Issues With VoIP Security?
The exchange of data packets opens up ports that, in turn, make the internal topology of a VoIP Solution visible. This vulnerability allows hackers to tunnel into the system and carry out exploits. Even secured SIP offers an encrypted tunnel that permits tapping in or intruding into the network. Other possible security issues with VoIP are:
- Denial Of Services- VoIP vulnerabilities can open the user network to (DoS) Denial of Service or (DDoS) Distributed Denial of Service attacks that jam the network and make it impossible to receive or make calls.
- Toll Fraud- Attackers can access an external line and make expensive international calls. It can rack up extra toll charges.
- Spamming– Spamming over the Internet or SPIT attacks can occur in which hackers may leave voice messages on IP phones.
- Identity Theft/VoIP Phishing – It is possible to hijack identities and steal money through VoIP phishing. Hackers may introduce malware or steal business data.
How To Improve VoIP Security?
There are some basic countermeasures to improve VoIP security. These are
- Use Of IPSEC, S/MIME, And TLS: It is an encryption mechanism that works at the lower layers. However, the drawback of the encryption mechanism is that its tasks are CPU intensive. Additionally, it also introduces latency that affects call quality.
- Another way to secure VoIP is to use device authentication and permit access only to known addresses.
- Segregation method – separation of voice and data using different logical networks is a possible way of VoIP Security.
- Use of anti-virus and anti-malware tools- To some extent, it is an age-long yet effective way to secure VoIP systems compared to other methods mentioned above. However, anti-virus and anti-malware tools are only partially adequate and reliable.
All these methods do not guarantee 100% VoIP security. It is where the Session Border Controller steps in and provides vastly improved security besides improving the quality of services and calls leading to user delight.
A VoIP network is very vulnerable without SBC! Secure it today with our customized SBC Solution.
What Is A Session Border Controller In VoIP?
Session Border Controller is a multi-purpose and indispensable solution from the security perspective. It acts as a firewall that ensures the security of the VoIP network against any breach or obtrusion of susceptible third parties. An SBC Solution secures the transmission of data packets by controlling the IP communication flows.
Let’s examine a few of the session border controller’s key responsibilities that explains how SBC secures VoIP.
- Session Border Controller Solution identifies and prevents DoS/DDoS attacks.
- It hides the internal network topology and keeps the internal network fully protected.
- VoIP SBC software plays a crucial role in network address traversal while fully encrypting all VoIP packets.
Moreover, a customized SBC Solution by Ecosmob Technologies is a one-stop destination regulating all forms of real-time communications, including voice, video, text chat, and collaboration sessions, with robust security features. You can learn the benefits of a customized Session Border Controller solution by sending your queries here. Our experts will guide you through it.
From the user perspective, Session Border Controller Solution works in various ways to deliver a superior experience:
- VoIP SBC Solutions normalize SIP and prevent overheads arising due to interoperability problems due to different flavors of SIPs.
- The Session Border Controller handles all known codecs and media transcoding. SBC is responsible for call admission control policies, handling voice packets, and prioritization.
- The presence of SBC in the network dramatically improves the quality of calls.
- Session Border Controller Solution also reduces the operation cost since it handles traffic routing over the minor cost route.
Also Read: How to Choose the Best VoIP Solutions Provider
Conclusion
Ecosmob Technologies provides you with the best in technology SBC solutions. To help you receive the maximum benefits of SBC, we offer various services, which include:
- A customized security system for your current VoIP network.
- A system that provides the utmost security and works seamlessly with your existing VoIP network.
To learn more about our Session Border Controller Solution offering or to discuss your requirement, drop an email to sales@ecosmob.com.